Ransomware Protection allows detection of processes that attempt to encrypt user's files using known algorithm that defines processes as a security threat. Ransomware is one of these processes. When entering a computer such malicious programs block access to user data and then demand ransom for decryption. They are considered among the most common malicious programs and cause great annual losses both to companies and ordinary users. The most common way of getting infected are bulk emails containing malicious files or a link to malware.
According to Doctor Web statistics, probability of restoring files compromised by encryption ransomware is only 10%, that is why the most efficient way of fighting it is to prevent the infection. Recently the number of users that have suffered such infection has decreased. However, the number of Dr.Web technical support requests for decryption reaches 1000 every month.
To open the Ransomware Protection window
1.Open Dr.Web menu ![]() , then select Security Center.
, then select Security Center.
2.In the open window, click Preventive Protection tile.
3.Make sure Dr.Web operates in administrator mode (the lock at the bottom of the program window is open ![]() ). Otherwise, click the lock
). Otherwise, click the lock ![]() .
.
4.Click the Ransomware Protection tile.
The component parameters can be adjusted if the the administrator of the central protection server, to which Dr.Web is connected, enables this option. |

Figure 55. Access to the Ransomware Protection component
In this section:
•Configuring reaction to application attempts to encrypt files
•Separate rules for certain applications
Dr.Web reaction to application attempts to encrypt a file
To configure Ransomware Protection parameters
1.Make sure Dr.Web operates in administrator mode (the lock at the bottom of the program window is open ![]() ). Otherwise, click the lock
). Otherwise, click the lock ![]() .
.
2.Click the Ransomware Protection tile. A component parameter window opens.
3.In the drop-down menu, select an action to be applied to all applications.
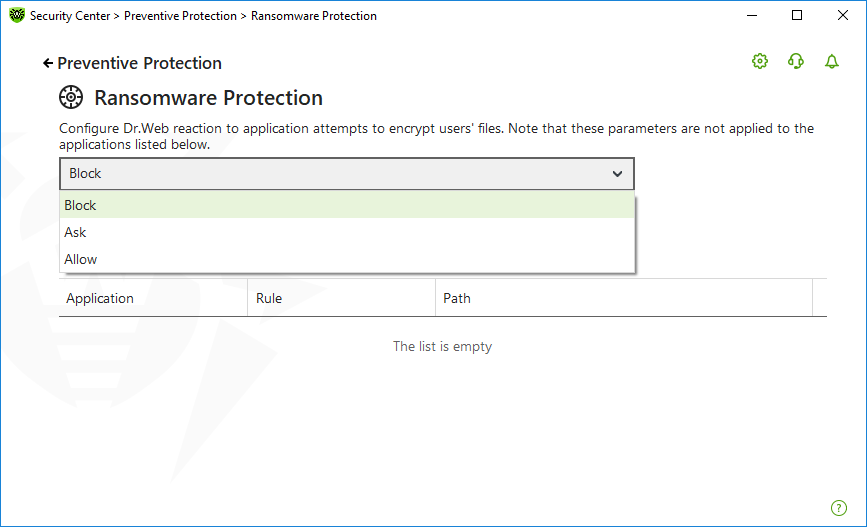
Figure 56. Selecting Dr.Web reaction
•Allow—all the applications are allowed to modify user's files.
•Block—all the applications are not allowed to encrypt user's files. This mode is enabled by default. When an application attempts to encrypt user's files the following notification will be shown:

Figure 57. Notification example with a blocked application attempt to modify user's files
•Ask—when an application attempts to encrypt a user's file, a notification appears, where you can prevent the encryption or ignore it:

Figure 58. Notification example with an application attempt to modify user's files
▫When clicking Fix button the process is blocked and moved to quarantine. Even if the application is restored from the quarantine it cannot be launched until the computer restart.
▫If you close the notification window, the application will not be neutralized.
Receiving notifications
If necessary, you can configure desktop notifications on Ransomware Protection actions.
See also:
Separate rules for certain applications
You can configure Ransomware Protection reaction on actions of certain applications. For this, add applications to the list and select a necessary reaction of the component. The following management elements are available to work with objects in the list:
•The button—add the application to the list of applications with separate rules.
•The button—delete the application from the list of applications with separate rules.
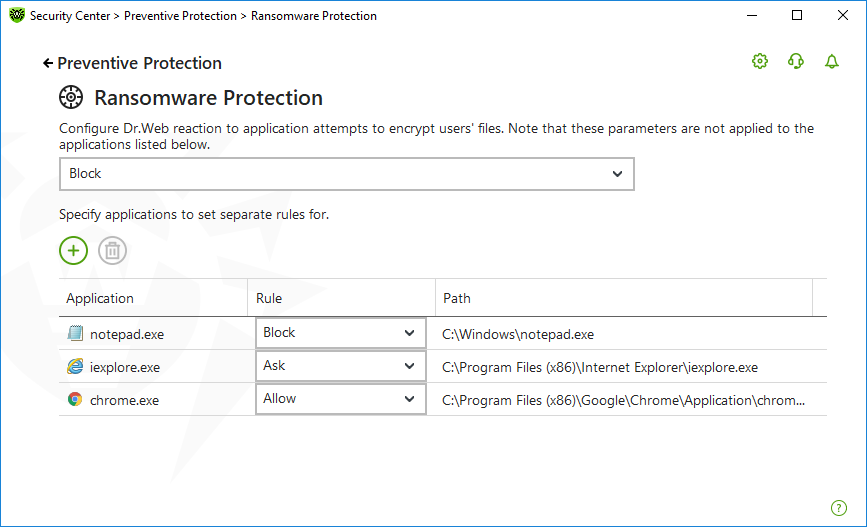
Figure 59. Applications not covered by component general rule
To add an application to the list
1.Click .
2.In the open window, click Browse and specify the path to the application executable file.

Figure 60. Selecting a rule for a certain application
3.Select a necessary component reaction from the drop-down list.
4.Click OK.
You can also change previously selected rule.
To change the Dr.Web reaction for applications with rules set
1.On the main window of the Ransomware Protection component, select the required application.
2.In the corresponding line in the Rule column select from the drop-down list the required reaction on application attempts to encrypt user's files.